In today's distributed workforce environment, protecting data across numerous devices has become a paramount concern for organisations of all sizes. As employees work from home offices, cafés, airports, and client sites, the traditional security perimeter has dissolved. Each laptop, tablet, and smartphone represents a potential point of failure where critical business information could be lost forever. Modern endpoint backup solutions address this challenge by automatically safeguarding data from every device in your organisation, ensuring business continuity regardless of where your team members work.
Understanding Endpoint Backup in Modern Business Contexts
Endpoint backup refers to the systematic process of copying and storing data from end-user devices such as desktops, laptops, mobile phones, and tablets to a secure location. Unlike traditional server-based backup approaches, endpoint backup solutions specifically target the devices employees use daily, protecting files that might never reach centralised servers.
The necessity for robust endpoint protection has intensified dramatically. Statistics indicate that nearly 60% of corporate data now resides on endpoints rather than in data centres. This shift reflects fundamental changes in how we work, collaborate, and store information.
The Distributed Data Challenge
Consider the typical knowledge worker's daily routine. They create presentations on their laptop, save research documents locally, download customer information for offline review, and store project files in their device's downloads folder. Many of these files never reach corporate servers or cloud collaboration platforms.
Common scenarios where endpoint data remains vulnerable include:
- Draft documents saved locally during travel without internet connectivity
- Email attachments downloaded for offline review
- Screenshots and notes captured during client meetings
- Configuration files and application settings unique to individual devices
- Cached data from cloud applications
When a device is lost, stolen, or suffers hardware failure, all this information disappears unless proper endpoint backup measures are in place. The consequences of inadequate endpoint protection extend beyond data loss to include compliance violations, intellectual property theft, and significant operational disruption.

Critical Components of Effective Endpoint Backup Systems
Implementing a comprehensive endpoint backup strategy requires understanding the essential features that separate basic file copying from enterprise-grade data protection. Modern solutions must balance security, usability, and performance whilst operating seamlessly in the background of users' daily workflows.
Automated Scheduling and Continuous Protection
Manual backup processes inevitably fail. Employees forget, postpone, or simply ignore backup prompts when facing pressing deadlines. Automated endpoint backup systems eliminate this human factor by running scheduled backups without user intervention.
Key automation capabilities include:
- Continuous data protection that monitors file changes in real-time
- Scheduled backups during off-peak hours to minimise performance impact
- Bandwidth throttling to prevent network congestion
- Automatic retry mechanisms for failed backup attempts
The most sophisticated systems employ intelligent scheduling that adapts to individual usage patterns, backing up data during periods of device inactivity whilst ensuring critical files receive immediate protection.
Encryption and Security Standards
Data travelling from endpoints to backup repositories traverses multiple networks, potentially including public Wi-Fi connections and shared infrastructure. Without proper encryption, this data becomes vulnerable to interception and theft.
| Security Feature | Purpose | Implementation Standard |
|---|---|---|
| In-transit encryption | Protects data during transmission | TLS 1.3 or higher |
| At-rest encryption | Secures stored backup data | AES 256-bit |
| Authentication | Verifies user identity | Multi-factor authentication |
| Access controls | Limits data visibility | Role-based permissions |
Beyond encryption, comprehensive endpoint backup solutions incorporate data sovereignty controls, allowing organisations to specify geographic storage locations to meet regulatory requirements. For businesses prioritising privacy, solutions like those offered by vBoxx enable organisations to maintain full control over their data whilst benefiting from robust backup infrastructure.
Centralised Management and Monitoring
IT administrators require visibility across the entire endpoint estate to ensure backup compliance and identify potential issues before they result in data loss. Centralised management consoles provide this oversight through unified dashboards displaying backup status, storage consumption, and policy compliance for every protected device.
Effective management platforms enable administrators to:
- Deploy backup agents remotely across multiple endpoints simultaneously
- Configure backup policies based on department, role, or device type
- Monitor backup success rates and identify devices with recurring failures
- Generate compliance reports demonstrating data protection coverage
- Adjust storage allocation and retention policies dynamically
This centralised approach proves particularly valuable for organisations with distributed teams, allowing IT departments to protect endpoints regardless of physical location.
Developing a Comprehensive Endpoint Backup Strategy
Creating an effective endpoint backup strategy extends beyond selecting technology. Organisations must align technical capabilities with business requirements, regulatory obligations, and operational realities to build a sustainable data protection programme.
Assessing Organisational Risk and Requirements
The first step involves understanding what data resides on endpoints and evaluating its criticality to business operations. Different departments and roles generate varying types of data with differing sensitivity levels and retention requirements.
Critical assessment questions include:
- Which departments handle sensitive customer data, intellectual property, or regulated information?
- What compliance frameworks govern data retention and protection in your industry?
- How quickly must data be recoverable following device loss or failure?
- What is the maximum acceptable data loss measured in hours or days?
Mapping these requirements creates a foundation for policy development. For instance, engineering teams with proprietary designs may require hourly backups with extended retention periods, whilst administrative staff might need only daily backups with shorter retention windows.
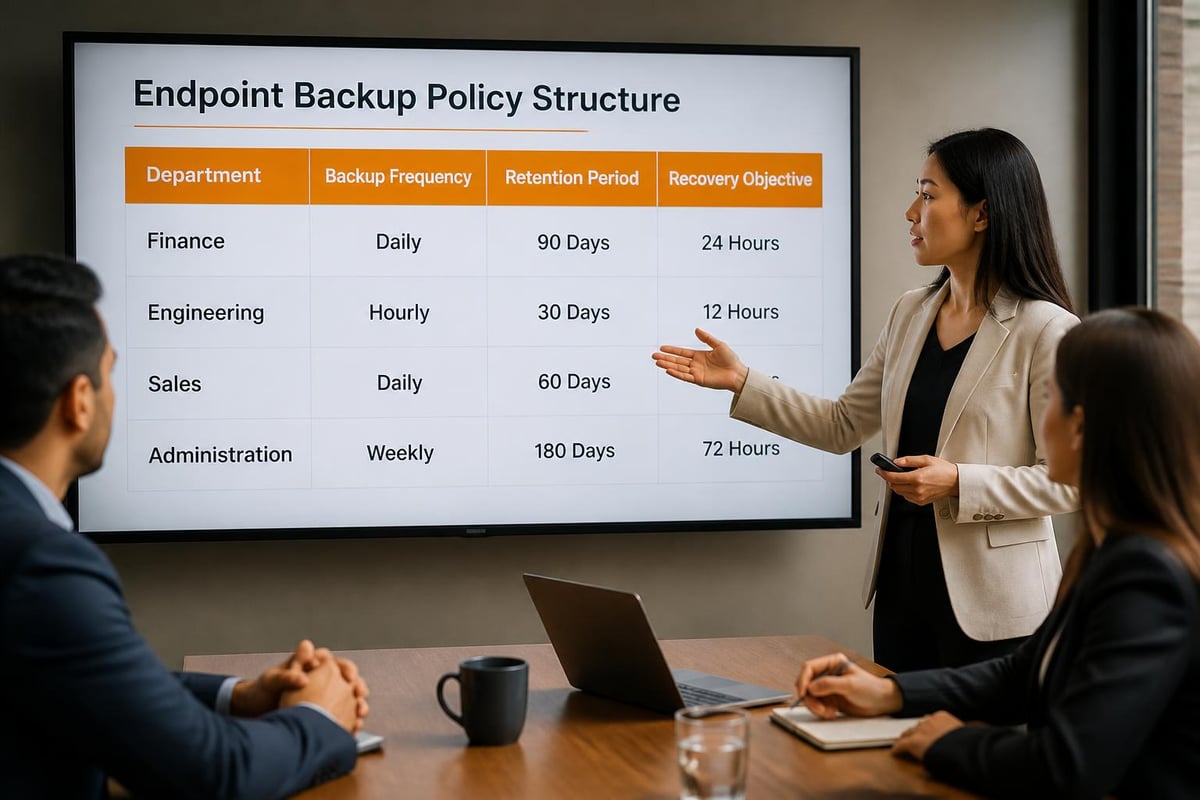
Creating Practical Backup Policies
Developing effective backup strategies requires balancing comprehensive protection with practical constraints around storage capacity, network bandwidth, and user experience. Policies must be enforceable, sustainable, and aligned with actual working patterns.
Consider implementing tiered policies based on data classification:
| Data Classification | Backup Frequency | Retention Period | Priority Level |
|---|---|---|---|
| Critical business data | Continuous or hourly | 90+ days | Highest |
| Standard documents | Daily | 30-60 days | Medium |
| Temporary files | Weekly | 7-14 days | Low |
| System configurations | Weekly | 30 days | Medium |
These policies should be documented, communicated clearly to users, and regularly reviewed to ensure they remain appropriate as business needs evolve. The goal is creating a framework that protects essential data without overwhelming storage systems or impeding employee productivity.
User Education and Adoption
Even the most sophisticated endpoint backup technology fails if users circumvent it or store data in unprotected locations. Successful implementation requires cultivating a culture where data protection is understood and valued rather than viewed as an IT-imposed burden.
Effective user education programmes should explain not just the "how" but the "why" of endpoint backup. Sharing real examples of how backups prevented data loss following device theft or ransomware attacks makes the value tangible. Providing clear guidance on what data requires protection and what's already safeguarded through other mechanisms prevents confusion and over-reliance on local storage.
Regular communications reinforcing best practices, coupled with metrics showing departmental backup compliance rates, encourage consistent participation. When employees understand that endpoint backup protects their work and simplifies device replacements, adoption increases naturally.
Implementation Considerations for Remote and Hybrid Workforces
The shift towards remote and hybrid working models has fundamentally altered the endpoint backup landscape. Traditional approaches designed for office-based employees with reliable, high-speed corporate network connections often fail when applied to distributed workforces operating across varied connectivity conditions.
Addressing Connectivity Challenges
Remote employees may work from locations with limited bandwidth, intermittent connectivity, or restrictive firewall configurations. Endpoint backup strategies for remote work environments must accommodate these constraints whilst maintaining adequate data protection.
Adaptive strategies include:
- Implementing incremental and delta backup technologies that transmit only changed data portions
- Configuring intelligent bandwidth management that adapts to available network capacity
- Enabling backup pause and resume functionality for interrupted connections
- Providing offline backup capabilities that queue data for transmission when connectivity resumes
- Supporting multiple backup destinations including local storage for rapid recovery
These capabilities ensure backups complete successfully regardless of network conditions, preventing the scenario where remote workers' data remains unprotected for extended periods due to connectivity limitations.
Mobile Device Integration
Modern workforces increasingly rely on smartphones and tablets as primary work devices. However, these platforms present unique challenges for endpoint backup implementation due to operating system restrictions, limited local storage, and varied usage patterns.
Comprehensive endpoint backup strategies must address mobile devices through:
- Cloud-native backup approaches that integrate with device-specific cloud services
- Selective backup of business-relevant data applications rather than entire devices
- Automated backup triggering when devices connect to Wi-Fi networks
- Minimal battery impact through optimised backup scheduling
- Secure containerisation separating business data from personal information
Successfully protecting mobile endpoints requires solutions that respect device limitations whilst ensuring business data receives adequate protection regardless of which device employees choose for specific tasks.

Advanced Capabilities and Emerging Trends
As cyber threats evolve and data volumes expand, endpoint backup solutions incorporate increasingly sophisticated capabilities that extend beyond basic file copying to comprehensive data resilience and security integration.
Ransomware Protection and Recovery
Ransomware attacks specifically target endpoints, encrypting local files and demanding payment for decryption keys. Traditional endpoint backup alone provides insufficient protection if ransomware encrypts backed-up versions along with original files. Advanced solutions incorporate ransomware-specific protections including immutable backups that cannot be modified or deleted, even by ransomware with administrative privileges.
Modern ransomware defences include:
- Version history maintaining multiple restore points to recover pre-infection states
- Behavioural analysis detecting unusual file modification patterns indicative of encryption
- Air-gapped backup copies isolated from network-accessible storage
- Automated alerts notifying administrators of potential ransomware activity
- Rapid recovery workflows enabling quick restoration of clean data versions
These capabilities transform endpoint backup from passive data copying into active defence against one of the most prevalent and damaging cyber threats facing organisations today.
Integration with Broader Security Ecosystems
Leading endpoint backup solutions no longer operate in isolation but integrate with broader security and IT management platforms. This integration enables coordinated responses to security incidents and streamlined administrative workflows.
Integration points include endpoint detection and response platforms, security information and event management systems, and IT service management tools. When backup systems detect suspicious activity, they can automatically trigger security investigations. Conversely, when security tools identify compromised devices, they can initiate immediate backups of uninfected data before isolation procedures commence.
For organisations seeking comprehensive data protection, exploring cloud storage and backup solutions that integrate multiple security layers provides enhanced resilience against diverse threat vectors.
Measuring Endpoint Backup Success and Compliance
Implementing endpoint backup represents just the beginning. Organisations must continuously monitor, measure, and optimise their programmes to ensure ongoing effectiveness and identify improvement opportunities.
Key Performance Indicators
Successful endpoint backup programmes track specific metrics that reveal system health and programme effectiveness. These measurements enable data-driven decisions about resource allocation, policy adjustments, and technology investments.
| Metric | Target Range | Significance |
|---|---|---|
| Backup success rate | >95% | Overall system reliability |
| Mean time to recovery | <2 hours | Operational impact of data loss |
| Endpoint coverage | 100% | Programme completeness |
| Storage efficiency | 3:1 deduplication ratio | Cost optimisation |
| Policy compliance | >98% | Risk management effectiveness |
Regular reporting on these indicators identifies trends requiring attention. A declining backup success rate might indicate network capacity issues, agent compatibility problems, or user interference requiring investigation and remediation.
Conducting Regular Recovery Testing
The ultimate measure of endpoint backup effectiveness is successful data recovery when needed. Organisations often discover backup failures only when attempting restoration during actual emergencies. Best practices for endpoint backup emphasise regular recovery testing to validate that backups are complete, accessible, and restorable within required timeframes.
Structured testing programmes should include:
- Monthly spot-checks recovering random files from various endpoints
- Quarterly full-device restoration tests simulating complete hardware failures
- Annual disaster recovery exercises testing organisation-wide endpoint recovery
- Documentation of recovery procedures ensuring consistent execution
- Post-test reviews identifying process improvements and training needs
These exercises not only validate technical capabilities but also familiarise IT staff with recovery procedures, reducing stress and errors during actual incidents.
Adapting to Evolving Requirements
Business needs, regulatory requirements, and technology capabilities continuously evolve. Endpoint backup strategies must adapt accordingly to remain effective and compliant. Regular programme reviews should assess whether current policies still align with business operations, whether new device types require protection, and whether emerging technologies offer improved capabilities.
Annual strategy reviews provide opportunities to evaluate vendor performance, assess whether storage capacity meets growing data volumes, and determine whether changing work patterns necessitate policy adjustments. Organisations experiencing rapid growth, mergers, or business model shifts may require more frequent reassessments to ensure endpoint backup programmes scale appropriately.
For businesses seeking expert guidance on implementing comprehensive backup strategies tailored to their specific requirements, a demonstration of integrated cloud solutions can provide valuable insights into how modern platforms address evolving data protection challenges.
Selecting the Right Endpoint Backup Solution
The endpoint backup market offers numerous solutions ranging from basic file synchronisation services to enterprise-grade data protection platforms. Selecting the appropriate solution requires carefully evaluating organisational requirements against vendor capabilities, considering both immediate needs and future growth.
Evaluation Criteria and Decision Framework
Comprehensive vendor evaluation should assess technical capabilities, operational requirements, and strategic alignment. Understanding endpoint backup functionality helps organisations develop evaluation criteria that reflect their specific contexts.
Critical evaluation dimensions include:
- Scalability: Can the solution grow from current endpoint counts to projected future requirements?
- Compatibility: Does it support all operating systems and device types in your environment?
- Performance: Will backup operations impact user productivity or network performance?
- Recovery flexibility: Can you restore individual files, folders, or complete system states?
- Security: Does it meet your encryption, access control, and compliance requirements?
- Management: How much administrative effort does ongoing operation require?
- Support: What service level agreements and support channels does the vendor provide?
Creating a weighted scoring matrix based on these criteria enables objective comparison across multiple vendors. Involving stakeholders from IT, security, compliance, and business units ensures evaluation criteria reflect diverse organisational priorities.
Total Cost of Ownership Considerations
Endpoint backup costs extend beyond initial licensing fees to include ongoing storage, administrative overhead, network infrastructure, and potential recovery expenses. Comprehensive cost analysis prevents unexpected budget impacts and enables accurate solution comparison.
Storage costs prove particularly significant, as data volumes typically grow 20-30% annually. Solutions offering efficient deduplication and compression reduce storage requirements, lowering long-term expenses. Additionally, consider bandwidth costs for organisations with usage-based internet connections, as continuous backup of numerous endpoints generates substantial data transfer volumes.
Administrative costs vary significantly based on solution sophistication. Highly automated platforms requiring minimal intervention may justify higher licensing costs through reduced administrative burden compared to solutions demanding constant monitoring and manual intervention.
Privacy and Data Sovereignty Considerations
For organisations handling sensitive information or operating under strict regulatory frameworks, data location and access controls become paramount selection criteria. Solutions storing backups in specific geographic regions help maintain compliance with data residency requirements, whilst those offering encryption key management ensure organisations retain exclusive access to their data.
Evaluating vendor security practices, audit certifications, and privacy policies provides insight into how seriously they approach data protection. Vendors with certifications such as ISO 27001, SOC 2, or industry-specific compliance frameworks demonstrate commitment to maintaining secure, compliant operations.
Organisations prioritising maximum control over their data should consider solutions enabling private cloud or hybrid deployment models, where backup infrastructure operates within organisational boundaries whilst benefiting from vendor-provided software and expertise.
Endpoint Backup in Regulated Industries
Certain industries face heightened regulatory scrutiny regarding data protection, retention, and availability. Healthcare, financial services, legal, and government sectors must ensure endpoint backup programmes satisfy specific compliance obligations beyond general data protection best practices.
Regulatory Requirements and Compliance Frameworks
Different regulatory frameworks impose varying requirements on endpoint data protection. The General Data Protection Regulation mandates specific security measures for personal data, whilst financial regulations often require defined retention periods and rapid recovery capabilities for business-critical information.
Common regulatory considerations include:
- Defined retention periods specifying minimum and maximum backup storage durations
- Audit trail requirements documenting backup activities and data access
- Encryption standards for data at rest and in transit
- Geographic restrictions on data storage locations
- Regular testing and validation of recovery capabilities
- Incident notification procedures for backup system compromises
Organisations operating across multiple jurisdictions must reconcile potentially conflicting requirements, implementing endpoint backup solutions flexible enough to accommodate various compliance demands simultaneously.
Documentation and Audit Preparedness
Regulatory compliance requires demonstrating adherence to requirements through comprehensive documentation and evidence. Endpoint backup programmes supporting compliance must generate detailed logs, reports, and audit trails documenting all protection activities.
Audit-ready programmes maintain:
- Policy documents detailing backup procedures, schedules, and responsibilities
- Configuration records showing system settings align with stated policies
- Activity logs capturing backup operations, successes, failures, and administrative actions
- Recovery test results demonstrating restoration capabilities
- Training records showing personnel understand data protection obligations
Regular internal audits using these materials identify gaps before external auditors or regulators discover them, enabling proactive remediation rather than reactive damage control.
Protecting endpoint data has evolved from an IT best practice to a business imperative as organisations embrace distributed work models and face escalating cyber threats. By implementing comprehensive endpoint backup strategies that balance security, usability, and compliance requirements, organisations safeguard their most valuable asset whilst enabling workforce flexibility. Whether you're establishing initial protection or enhancing existing capabilities, partnering with experienced providers ensures your backup infrastructure meets current demands whilst adapting to future challenges. vBoxx delivers secure, sustainable cloud solutions designed to protect your business data with privacy-first architecture and green hosting practices that align technology investments with environmental responsibility.



