In today’s digital landscape, businesses exchange sensitive information at unprecedented volumes. Financial reports, legal contracts, intellectual property, and customer data move between teams, partners, and clients daily. Without proper safeguards, this constant flow of critical information creates vulnerabilities that can lead to data breaches, compliance failures, and reputational damage. A secure document sharing platform provides the foundation for protecting these assets whilst maintaining the collaboration capabilities modern organisations require.
Why Traditional File Sharing Methods Fail Businesses
Email attachments and consumer-grade file sharing services were never designed to meet enterprise security requirements. When staff members send confidential documents via personal email accounts or free cloud storage platforms, organisations lose visibility and control over their most sensitive assets.
The risks extend beyond simple unauthorised access. Traditional methods lack audit trails, making it impossible to track who accessed documents, when they were viewed, or whether they were forwarded to unauthorised recipients. This creates compliance nightmares for organisations subject to GDPR, financial regulations, or industry-specific data protection requirements.
Common vulnerabilities in traditional file sharing include:
- No encryption for data in transit or at rest
- Inability to revoke access after documents are shared
- Lack of version control leading to conflicting document copies
- Missing activity logs for compliance auditing
- No integration with identity management systems
- Vulnerable to phishing attacks and credential theft
Studies show that secure file-sharing solutions have become essential as distributed work environments increase the attack surface for data breaches. Each unsecured sharing method represents a potential entry point for malicious actors.

Essential Features Every Secure Document Sharing Platform Must Provide
Selecting the right platform requires understanding which security capabilities are non-negotiable versus those that offer additional convenience. A robust secure document sharing platform must deliver comprehensive protection across multiple layers whilst remaining accessible to users.
End-to-End Encryption
Encryption serves as the cornerstone of document security. True end-to-end encryption ensures that documents remain encrypted during upload, storage, and download. Only authorised users with proper decryption keys can access the content, meaning even the platform provider cannot view your sensitive information.
Look for platforms that employ AES-256 encryption standards for data at rest and TLS 1.3 for data in transit. This military-grade protection ensures that intercepted data remains unreadable without authorisation.
Granular Access Controls
Not every team member requires the same level of access to shared documents. A secure document sharing platform should offer detailed permission settings that allow administrators to define precisely who can view, edit, download, print, or share specific documents.
| Permission Level | View | Edit | Download | Share | Delete |
|---|---|---|---|---|---|
| Viewer | ✓ | ✗ | ✗ | ✗ | ✗ |
| Editor | ✓ | ✓ | ✓ | ✗ | ✗ |
| Manager | ✓ | ✓ | ✓ | ✓ | ✗ |
| Administrator | ✓ | ✓ | ✓ | ✓ | ✓ |
Time-limited access represents another crucial capability. The ability to automatically revoke access after a specified period ensures that shared documents don’t remain accessible indefinitely, reducing the window of vulnerability for sensitive information.
Comprehensive Audit Trails
Compliance requirements and security investigations both demand detailed activity logs. Every action taken on shared documents should be recorded, including who accessed files, when they were opened, what changes were made, and whether documents were downloaded or shared externally.
These audit trails provide invaluable evidence during security incidents and simplify compliance reporting for regulated industries. Best practices for file sharing emphasise the importance of maintaining detailed logs as part of a comprehensive security strategy.
Implementation Strategies for Maximum Security
Deploying a secure document sharing platform requires more than simply purchasing software. Organisations must approach implementation systematically to ensure security measures are properly configured and adopted across the business.
Conducting a Security Assessment
Begin by mapping your current document sharing practices. Identify all locations where sensitive documents are stored, all methods currently used for sharing, and all types of sensitive information your organisation handles. This assessment reveals gaps in your current approach and helps prioritise security improvements.
Key questions to answer during assessment:
- Which departments handle the most sensitive information?
- What compliance requirements apply to your document handling?
- How many external parties regularly receive confidential documents?
- What existing security infrastructure can integrate with a new platform?
- Which document types pose the greatest risk if compromised?
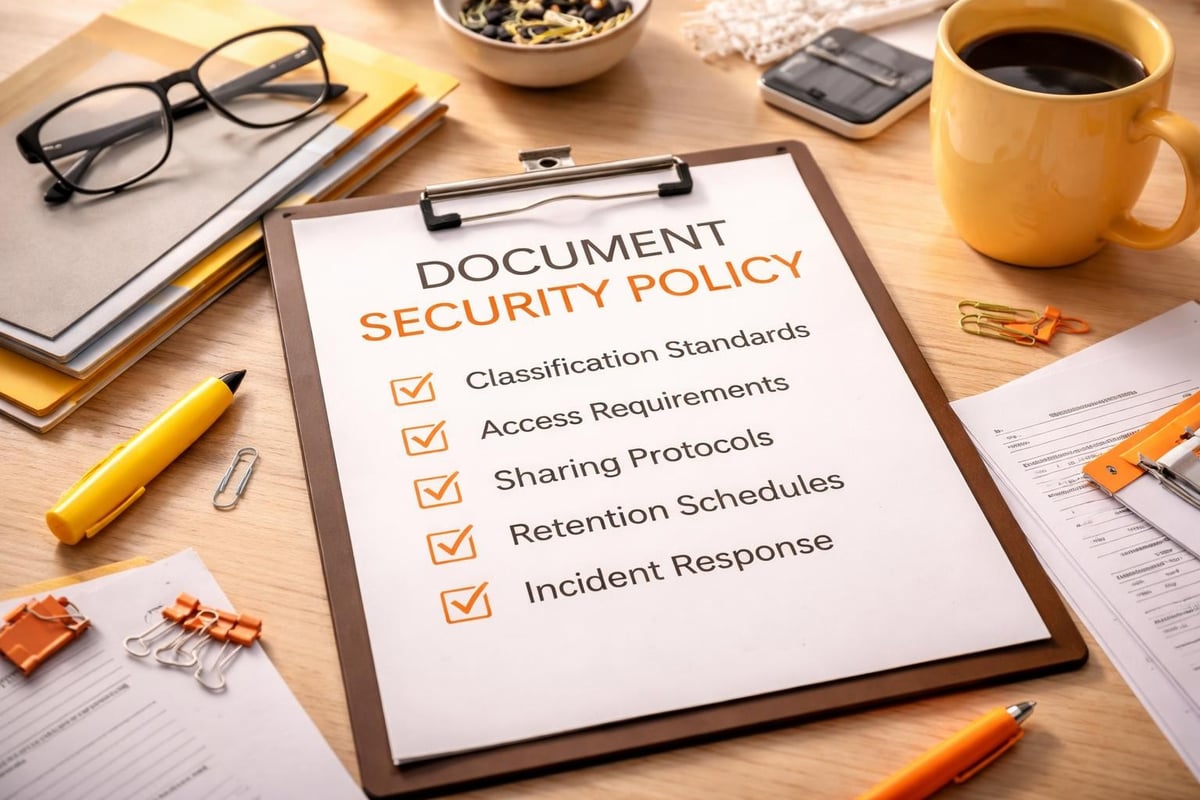
Establishing Security Policies
Technology alone cannot secure documents without clear policies governing their use. Develop comprehensive guidelines that define acceptable sharing practices, specify which document types require additional protection, and outline procedures for handling security incidents.
Your policy framework should address password requirements, multi-factor authentication mandates, permitted sharing methods, and consequences for policy violations. These guidelines create accountability and ensure consistent security practices across the organisation.
Advanced Security Capabilities for High-Risk Environments
Certain industries face elevated security requirements due to the sensitivity of their data or strict regulatory frameworks. Healthcare providers, financial institutions, legal firms, and government contractors need security features that exceed standard business requirements.
Zero-Knowledge Architecture
Zero-knowledge systems ensure that the platform provider has no access to encryption keys or unencrypted data. This architecture provides the highest level of privacy, guaranteeing that only authorised users can decrypt and access shared documents. Even in the event of a platform breach, encrypted data remains protected.
Data Loss Prevention Integration
A sophisticated secure document sharing platform integrates with data loss prevention (DLP) systems to automatically detect and prevent unauthorised sharing of sensitive information. These systems scan documents for patterns matching credit card numbers, personal identification numbers, or proprietary information, blocking transmission when violations are detected.
Geographic Data Residency Controls
For organisations subject to data sovereignty requirements, the ability to specify where data is physically stored becomes critical. Some regulations mandate that certain information types must remain within specific geographic boundaries. Advanced platforms offer granular controls over data location, ensuring compliance with regional requirements.
The importance of legal document sharing security demonstrates how regulated industries require platform capabilities beyond basic encryption and access controls.
User Authentication and Identity Management
Even the most secure platform becomes vulnerable when authentication mechanisms are weak. Robust identity verification ensures that only legitimate users gain access to shared documents whilst preventing unauthorised entry attempts.
Multi-Factor Authentication Requirements
Multi-factor authentication (MFA) adds critical protection by requiring users to verify their identity through multiple independent methods. Beyond passwords, users must provide additional verification such as time-based codes, biometric data, or hardware security keys.
Common MFA methods ranked by security level:
| Method | Security Level | User Convenience | Implementation Cost |
|---|---|---|---|
| SMS Codes | Low | High | Low |
| Authentication Apps | Medium | High | Low |
| Hardware Tokens | High | Medium | Medium |
| Biometric Verification | Very High | High | High |
| FIDO2 Security Keys | Very High | Medium | Medium |
Single Sign-On Integration
Integrating your secure document sharing platform with existing identity management systems streamlines access whilst maintaining security. Single sign-on (SSO) reduces password fatigue, minimises the number of credentials users must manage, and provides centralised control over access privileges.
SSO integration also simplifies offboarding procedures. When employees leave the organisation, administrators can revoke access across all integrated systems simultaneously rather than managing individual platform credentials.
Collaboration Features That Maintain Security
Security and productivity need not be opposing forces. Modern platforms prove that robust protection can coexist with the collaboration features teams require for effective work.
Real-Time Co-Editing with Version Control
Secure platforms enable multiple users to work on documents simultaneously whilst maintaining complete version histories. This capability prevents the confusion of multiple document copies whilst ensuring that organisations can restore previous versions if errors occur or unauthorised changes are made.
Version control also serves security purposes by documenting all modifications and allowing security teams to identify when sensitive information was added, modified, or removed from shared documents.
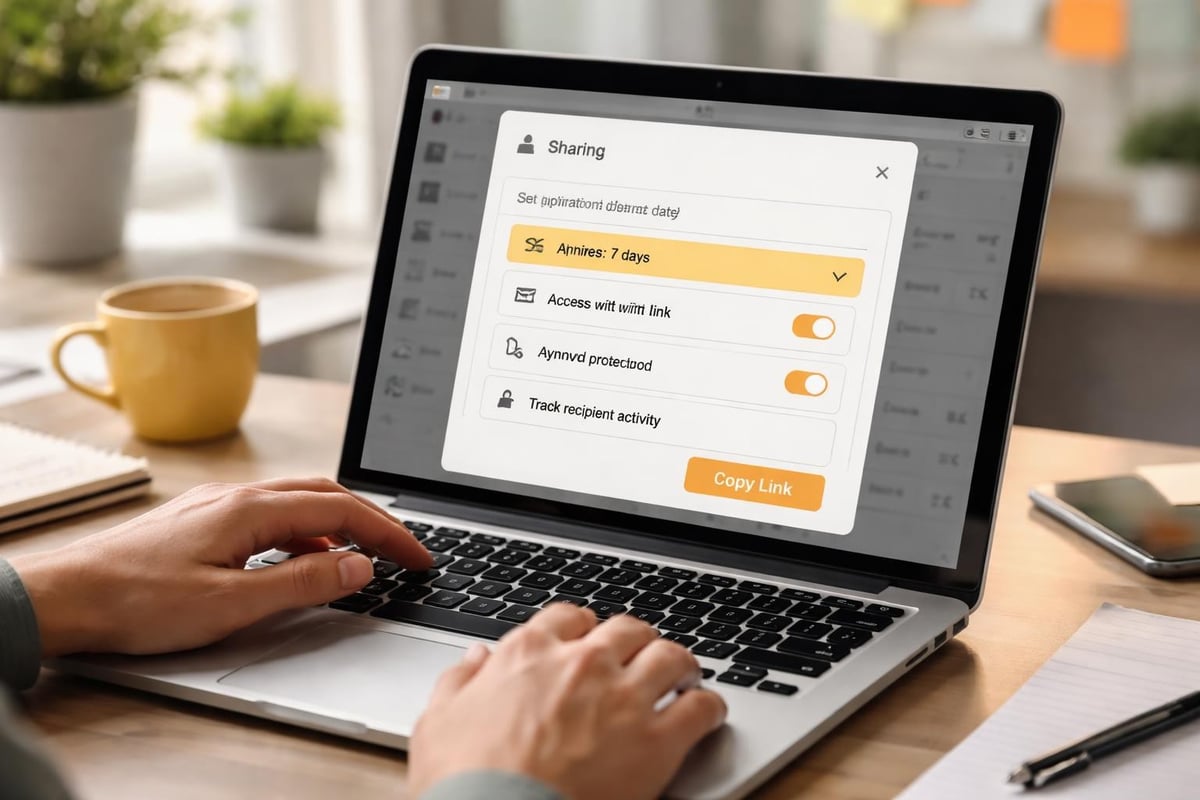
Secure External Sharing Links
Sharing documents with clients, partners, or vendors requires special consideration. Rather than attaching files to emails or using consumer platforms, a secure document sharing platform generates protected links with configurable security parameters.
These links can be password-protected, time-limited, and restricted to specific email addresses. Download limits prevent recipients from distributing documents beyond intended recipients, whilst link expiration ensures access doesn’t persist indefinitely.
For organisations looking to experience these capabilities firsthand, a demonstration of all-in-one solutions can provide valuable insights into how modern platforms balance security with usability.
Compliance and Regulatory Considerations
Industries face varying regulatory requirements that dictate how documents must be handled, stored, and shared. A compliant secure document sharing platform must address these requirements whilst providing documentation for audit purposes.
GDPR Compliance Features
The General Data Protection Regulation imposes strict requirements on organisations handling personal data of EU citizens. Compliant platforms must offer capabilities supporting data subject rights, including the ability to locate all instances of an individual’s data, export that data in portable formats, and permanently delete information when requested.
Data processing agreements, encryption standards, and breach notification capabilities all contribute to GDPR compliance. Platforms should document their security measures and provide tools for demonstrating compliance during regulatory audits.
Industry-Specific Requirements
Financial services firms must comply with regulations like SOX and PCI-DSS, which mandate specific security controls and audit trails. Healthcare organisations face HIPAA requirements governing patient information protection. Legal firms must maintain client confidentiality whilst meeting professional conduct standards.
Understanding secure document sharing practices specific to your industry ensures your chosen platform meets applicable regulatory requirements without requiring extensive customisation.
Performance and Scalability Considerations
Security features must not compromise platform performance or limit organisational growth. Enterprise-grade platforms balance robust protection with the speed and capacity businesses require.
Upload and Download Speeds
Large documents, particularly multimedia files or technical drawings, require efficient transfer capabilities. Platforms should support parallel uploads, resumable transfers, and optimised compression to minimise time spent waiting for file operations to complete.
Network optimisation through content delivery networks (CDNs) ensures that users in different geographic locations experience consistent performance regardless of where data is physically stored.
Storage Capacity and Expansion
Organisations accumulate documents continuously, requiring platforms that scale seamlessly as storage requirements grow. Look for solutions offering flexible storage tiers that expand automatically without requiring manual intervention or causing service interruptions.
Deduplication technologies reduce storage requirements by identifying and eliminating redundant copies of identical files, maximising available capacity whilst reducing costs.
Mobile Access Security
Modern work occurs across devices, requiring platforms that extend security to smartphones and tablets without compromising protection. Mobile security introduces unique challenges that demand specialised solutions.
Device Management Integration
Mobile device management (MDM) integration allows organisations to enforce security policies on smartphones and tablets accessing shared documents. These policies can require device encryption, prevent screenshots of sensitive documents, and remotely wipe corporate data if devices are lost or stolen.
Containerisation separates corporate documents from personal data on employee devices, ensuring that business information remains protected whilst respecting employee privacy.
Offline Access Controls
Some platforms allow users to cache documents locally for offline access, creating potential security vulnerabilities if devices are compromised. Secure implementations encrypt cached data, automatically purge offline copies after specified periods, and prevent offline documents from being shared outside the platform.
Current evaluations of business cloud storage services highlight the growing importance of mobile security features as remote work becomes permanent for many organisations.
Monitoring and Incident Response
Even with comprehensive preventive measures, organisations must prepare for potential security incidents. Effective monitoring and rapid response capabilities minimise damage when breaches occur.
Real-Time Security Alerts
Automated monitoring systems should detect suspicious activities such as mass downloads, unusual access patterns, or login attempts from unexpected locations. Real-time alerts enable security teams to investigate potential threats before significant damage occurs.
Critical activities requiring immediate alerts:
- Multiple failed login attempts
- Access from high-risk geographic locations
- Bulk document downloads by single users
- Sharing of highly sensitive documents externally
- Changes to critical security settings
- Unusual access times outside normal business hours
Incident Response Procedures
When security events occur, predefined response procedures ensure consistent, effective action. Documentation should specify who must be notified, what containment measures to implement, how to preserve evidence for investigation, and when external parties like legal counsel or law enforcement should be engaged.
Regular incident response drills help teams identify procedural gaps and ensure staff understand their roles during security events. These exercises also validate that platform security features function as expected during actual incidents.
Integration With Existing Business Systems
Isolated platforms create inefficiencies and potential security gaps. A secure document sharing platform should integrate seamlessly with existing business tools, creating unified workflows whilst maintaining consistent security policies.
CRM and Project Management Connections
Integrating document sharing with customer relationship management systems ensures that all client-related documents are associated with appropriate records. Project management integrations connect deliverables, specifications, and communications with project timelines, improving organisation whilst maintaining security.
These integrations eliminate the need to duplicate documents across multiple systems, reducing the risk that unsecured copies proliferate across the organisation. Reviewing options through platforms like vBoxx’s file management solution demonstrates how integrated approaches simplify security administration.
Email System Integration
Rather than encouraging users to attach documents to emails, integrated platforms enable sharing through secure links generated directly from email clients. This approach maintains the familiar email workflow whilst ensuring documents remain protected by platform security features.
Email integration also facilitates automatic archiving of shared documents, ensuring compliance with retention policies and creating comprehensive audit trails of all business communications.
Cost Considerations and ROI Analysis
Implementing a secure document sharing platform represents a significant investment requiring careful financial analysis. Understanding both direct costs and potential savings helps justify expenditure to stakeholders.
Direct Implementation Costs
Platform licensing represents the most obvious expense, with costs varying based on user count, storage requirements, and feature complexity. Additional expenses include initial configuration, user training, and potential customisation to meet specific organisational requirements.
Migration costs cover the effort required to transfer existing documents from current storage locations to the new platform whilst ensuring proper organisation and security classification.
Risk Mitigation Value
The financial impact of data breaches extends far beyond immediate response costs. Regulatory fines, legal settlements, customer notification expenses, and reputational damage create substantial long-term financial consequences. Recent data breaches have cost organisations millions in direct expenses and lost business opportunities.
A robust secure document sharing platform reduces breach probability, potentially preventing losses that dwarf implementation costs. This risk reduction provides quantifiable value when calculating return on investment.
Training and User Adoption Strategies
The most sophisticated security platform fails if users bypass it through convenience shortcuts. Successful implementation requires comprehensive training and change management to ensure consistent adoption across the organisation.
Role-Based Training Programs
Different organisational roles require different levels of platform knowledge. Administrators need deep technical understanding of security configurations and policy management. Regular users require practical training on everyday tasks like sharing documents securely and managing permissions. Executives might need only high-level overviews focused on strategic benefits and compliance implications.
Tailoring training to specific roles improves relevance and increases engagement whilst ensuring each user develops appropriate expertise for their responsibilities. Guidance from resources like Zoho’s secure document sharing practices can inform training content development.
Ongoing Education and Support
Security threats and platform capabilities evolve continuously, requiring ongoing education beyond initial implementation training. Regular updates about new features, emerging threats, and refined security practices keep users informed and engaged.
Establishing accessible support channels encourages users to seek assistance rather than developing insecure workarounds when they encounter difficulties. Responsive support teams can identify recurring issues that might indicate training gaps or platform configuration problems.
Green Hosting and Sustainable Infrastructure
Environmental considerations increasingly influence technology decisions as organisations recognise their responsibility for sustainable operations. Secure document sharing platforms can deliver robust protection whilst minimising environmental impact through thoughtful infrastructure choices.
Energy-Efficient Data Centres
Platform providers using renewable energy sources and energy-efficient cooling systems reduce the carbon footprint associated with document storage and sharing. Organisations committed to sustainability should prioritise providers demonstrating environmental responsibility through measurable initiatives.
Geographic placement of data centres affects both performance and environmental impact. Facilities in regions with naturally cool climates require less energy for cooling, whilst those powered by local renewable sources further reduce environmental impact.
Data Optimisation for Resource Efficiency
Compression technologies, deduplication, and intelligent archiving reduce storage requirements, decreasing the physical infrastructure needed to support document sharing platforms. These optimisations deliver environmental benefits whilst potentially reducing costs through more efficient resource utilisation.
Platforms that automatically identify and archive rarely accessed documents to lower-tier storage reduce the active computing resources required, further decreasing energy consumption without compromising security or accessibility when documents are eventually needed.
Future Trends in Secure Document Sharing
Technology evolution continually introduces new capabilities and challenges for secure document sharing. Understanding emerging trends helps organisations prepare for future requirements and evaluate platforms based on long-term viability rather than current features alone.
Artificial Intelligence for Security Enhancement
Machine learning algorithms increasingly detect anomalous behaviour patterns that might indicate security threats. These systems establish baselines for normal user activity, then flag deviations that could represent compromised accounts or insider threats.
AI-powered classification systems can automatically identify sensitive information within documents, applying appropriate security controls without requiring manual review. This automation ensures consistent security whilst reducing administrative burden.
Blockchain for Audit Trail Integrity
Blockchain technology offers tamper-proof audit trails by creating immutable records of all document activities. Each action generates a blockchain entry that cannot be altered retroactively, providing absolute confidence in log integrity for compliance and legal purposes.
Whilst still emerging, blockchain integration represents a potential solution for industries with stringent audit requirements or those facing significant insider threat risks.
Quantum-Resistant Encryption
As quantum computing capabilities advance, current encryption standards may become vulnerable to new attack methods. Forward-thinking platforms are beginning to implement quantum-resistant encryption algorithms that will maintain protection even as computing capabilities evolve.
Organisations handling highly sensitive information with long-term security requirements should monitor developments in post-quantum cryptography and consider migration timelines to quantum-resistant platforms.
Implementing a secure document sharing platform requires careful evaluation of security features, compliance requirements, and organisational workflows to ensure comprehensive protection without sacrificing productivity. The right platform delivers robust encryption, granular access controls, detailed audit trails, and seamless integration whilst supporting sustainable infrastructure practices. vBoxx provides secure cloud solutions designed specifically for businesses requiring uncompromising data protection combined with environmental responsibility, delivering the comprehensive security infrastructure modern organisations need to protect their most valuable information assets.



