Finding the right secure email solution for your business requires careful consideration of privacy features, encryption standards, and practical functionality. In particular, while Proton has established itself as a leading privacy-focused email provider, many organisations seek alternatives that better align with their specific operational requirements, budget constraints, or integration preferences. Therefore, understanding the landscape of secure email providers helps businesses make informed decisions about protecting their communications while also maintaining productivity and ensuring compliance with data protection regulations.
Understanding the Need for Secure Email Alternatives
The demand for privacy-focused email services has grown substantially as businesses recognise the critical importance of protecting sensitive communications. Many organisations initially gravitate towards well-known providers but subsequently discover that their unique requirements call for different solutions.
Key factors driving the search for a proton alternative include:
- Specific compliance requirements within regulated industries
- Integration capabilities with existing business infrastructure
- Budget considerations for small to medium-sized enterprises
- Advanced collaboration features beyond basic email functionality
- Regional data residency requirements

Different providers excel in distinct areas. Some prioritise maximum encryption strength, whilst others focus on user experience or seamless integration with productivity tools. Secure email services form the foundation of modern business communication security, protecting against increasingly sophisticated cyber threats.
Evaluating Your Organisation’s Priorities
Before exploring alternatives, organisations must establish clear priorities. In particular, a healthcare provider requires different features than a technology startup or financial services firm. As a result, security, compliance, scalability, and usability requirements can vary significantly between industries. Moreover, defining these priorities early helps ensure that the selected solution aligns with specific operational and regulatory needs.
Consider these essential evaluation criteria:
- End-to-end encryption standards and implementation methods
- Data sovereignty and server location preferences
- User interface complexity versus security trade-offs
- Scalability for growing team requirements
- Cost structure aligned with organisational budget
- Support quality and response time guarantees
The right solution balances robust security with practical usability. In particular, overly complex systems lead to user frustration and potential security workarounds, whilst insufficient protection exposes sensitive information to risk. As a result, organisations must carefully evaluate both usability and security when selecting a platform. Moreover, achieving this balance helps ensure consistent adoption and stronger overall data protection.
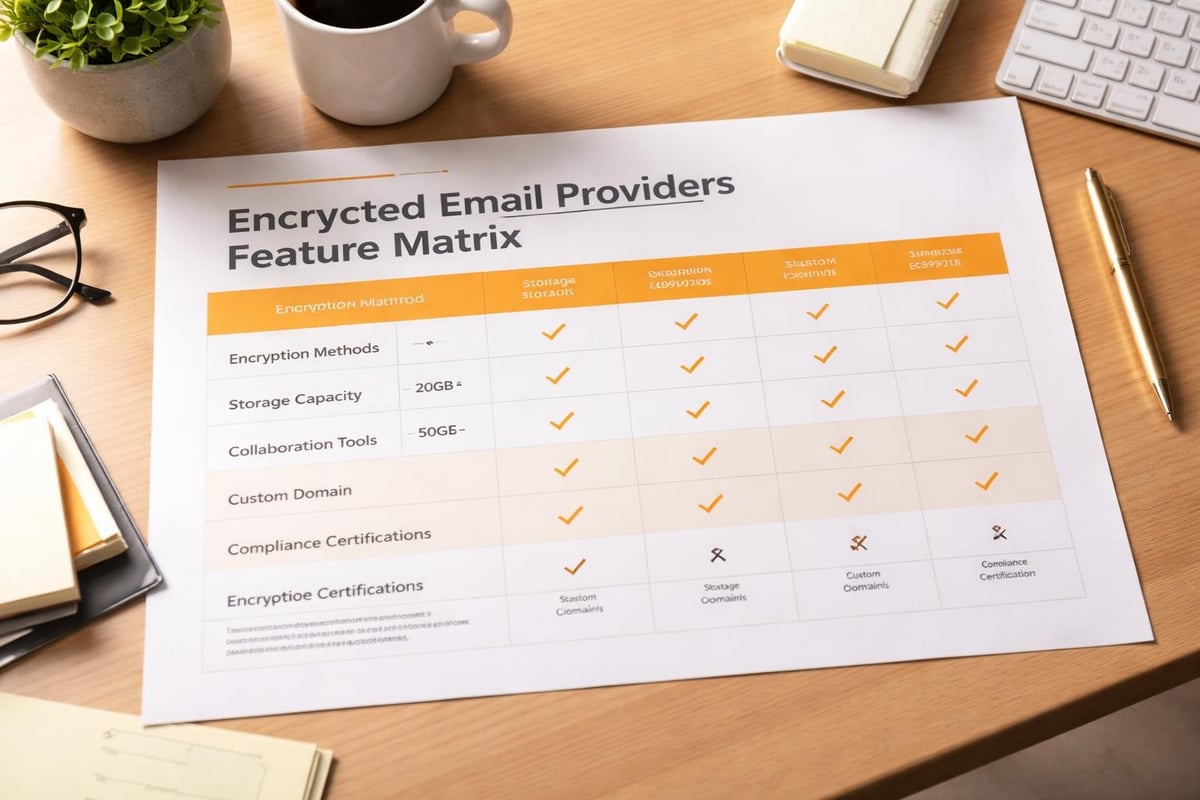
Leading Secure Email Providers in 2026
The secure email market has matured significantly, offering businesses diverse options beyond the standard consumer-focused platforms. In particular, each provider brings unique strengths to address specific organisational needs. Moreover, this diversity allows organisations to select solutions aligned with their security, compliance, and usability priorities. As a result, businesses can implement more tailored and effective communication strategies.
Privacy-Focused Business Solutions
Several providers have emerged as strong contenders for organisations seeking a proton alternative with enhanced business capabilities. These services maintain strict privacy standards whilst offering features that support modern workplace collaboration.
Hushmail stands out for healthcare and professional services firms. This provider specialises in HIPAA-compliant communications, offering encrypted email alongside e-signable forms that streamline administrative workflows. Their focus on regulatory compliance makes them particularly valuable for medical practices, legal firms, and financial advisors handling sensitive client information.
Tutanota provides comprehensive encryption covering not just email content but also contact lists and calendar entries. Their German-based infrastructure appeals to organisations prioritising European data protection standards. The service offers competitive pricing tiers suitable for small businesses whilst maintaining enterprise-grade security protocols.
| Provider | Primary Strength | Best For | Starting Price |
|---|---|---|---|
| Hushmail | Healthcare compliance | Medical/legal professionals | £8.99/month |
| Tutanota | Full-suite encryption | Privacy-conscious SMEs | £1.00/month |
| Mailfence | Digital signatures | Document-heavy workflows | £2.50/month |
| Posteo | Environmental focus | Sustainability-minded businesses | £1.00/month |
Feature-Rich Alternatives
Beyond basic encrypted email, modern organisations require integrated tools supporting collaboration, project management, and client communications. In response, several providers have expanded their offerings to meet these broader needs.
For example, Mailbox.org delivers a comprehensive suite including calendar, cloud storage, and office applications alongside encrypted email. In particular, this German provider emphasises sustainability and transparency, publishing detailed security audits and operational reports. Moreover, its feature set rivals mainstream productivity platforms whilst maintaining strict privacy protections.
Additionally, the platform supports custom domain integration, making it suitable for businesses wanting professional email addresses with robust security. As a result, its pricing remains accessible for small teams whilst also offering scalability for growing organisations.
Technical Considerations for Business Email Security
Selecting a proton alternative requires understanding the technical foundations that protect your communications. In particular, not all encryption implementations provide equivalent security, and therefore, compatibility issues can undermine even the strongest security measures. Consequently, organisations must carefully evaluate both security standards and interoperability to ensure reliable and effective protection.
Encryption Standards and Protocols
End-to-end encryption (E2EE) represents the gold standard for email security, ensuring only intended recipients can read message contents. However, implementation details significantly impact practical security levels.
Modern secure email providers typically employ:
- PGP (Pretty Good Privacy) for message encryption
- AES-256 for data-at-rest protection
- TLS/SSL for transport layer security
- Zero-knowledge architecture preventing provider access to content
Understanding these technical distinctions helps organisations evaluate provider claims. Some services offer encryption only for messages between users on the same platform, limiting protection when communicating with external contacts. True E2EE maintains security regardless of recipient email provider.
Integration and Compatibility Challenges
One frequent concern when evaluating alternatives involves integration with existing business tools. In particular, organisations using customer relationship management systems, project management platforms, or document management solutions need email services that connect seamlessly with these critical applications. Therefore, selecting a solution with strong integration capabilities ensures smooth workflows and minimises operational disruption.
Key integration points to evaluate:
- Calendar synchronisation across devices and platforms
- Contact management and address book functionality
- API availability for custom application development
- Mobile application quality and feature parity
- Migration tools for transitioning from existing providers
Some organisations explore various alternatives to find the optimal balance between security and operational efficiency. The transition cost in terms of time, training, and potential productivity disruption must factor into decision-making alongside security benefits.
Cost-Benefit Analysis for Businesses
Budget constraints influence every technology decision, particularly for small to medium-sized enterprises balancing security needs against limited resources. As a result, secure email providers span a wide pricing spectrum, ranging from free personal tiers to premium enterprise solutions. Therefore, organisations must carefully evaluate cost against features to ensure they achieve the right balance between affordability and security.
Understanding True Total Cost
Beyond subscription fees, organisations must account for implementation costs, ongoing administration, user training, and potential productivity impacts during transition periods.
| Cost Category | Typical Range | Key Considerations |
|---|---|---|
| Per-user subscription | £1-£20/month | Features increase with price tiers |
| Migration services | £500-£5,000 | Complexity depends on data volume |
| Training requirements | £200-£2,000 | User technical proficiency matters |
| Lost productivity | Variable | Transition period efficiency reduction |
| Ongoing administration | 2-10 hours/month | Management complexity varies by provider |
Free and low-cost options serve solo practitioners and very small teams effectively. However, growing businesses often encounter limitations requiring upgrades. Planning for scalability from the outset prevents disruptive migrations as team size increases.
Value Proposition Assessment
The cheapest option rarely delivers optimal value. Instead, organisations must weigh security benefits, feature richness, and support quality against cost differences. For example, a slightly more expensive provider offering superior integration capabilities might reduce overall operational costs through improved efficiency.
Furthermore, consider the potential costs of security breaches when evaluating provider pricing. In fact, data breach expenses typically far exceed email service costs, thereby making robust security an investment rather than an expense. Consequently, regulatory penalties, customer trust erosion, and remediation costs can devastate organisations lacking adequate protection.
Business-Specific Use Cases
Different industries and organisational structures benefit from tailored approaches to secure email. In particular, a proton alternative ideal for one business may prove unsuitable for another with different operational requirements. Therefore, organisations must assess their specific needs and use cases to ensure they select the most appropriate solution.
Professional Services Firms
Legal practices, accounting firms, and consultancies handle exceptionally sensitive client information requiring maximum confidentiality. These organisations prioritise:
- Attorney-client privilege protection through robust encryption
- Document retention policies aligned with professional standards
- E-signature capabilities for contract execution
- Audit trails demonstrating compliance with ethical obligations
Professional services often justify premium pricing for providers offering specialised compliance features. In particular, the ability to demonstrate security measures to clients becomes a competitive advantage in industries where trust forms the business foundation. As a result, organisations can strengthen client confidence and differentiate themselves in competitive markets. Moreover, this emphasis on transparency and compliance supports long-term business relationships.
Technology and Creative Agencies
Digital agencies and software development firms need secure email integrated with project management workflows and client collaboration platforms. Their priorities differ substantially from professional services:
- Large file attachment support for design assets
- Integration with version control and project tracking systems
- Team collaboration features beyond basic email
- Developer-friendly APIs for custom tooling
These organisations often seek online storage solutions that complement their email services, creating unified secure communication and file-sharing ecosystems. The technical sophistication of users means complex security measures cause less friction than in general business contexts.

Healthcare and Medical Practices
Medical organisations face strict regulatory requirements making compliance non-negotiable. In particular, HIPAA in the United States, GDPR in Europe, and similar regulations worldwide mandate specific security controls for patient communications. As a result, healthcare providers must implement robust safeguards to protect sensitive patient data. Moreover, failure to comply can lead to significant legal and financial consequences, as well as loss of patient trust.
Healthcare-focused providers offer:
- Business Associate Agreements establishing compliance relationships
- Automatic encryption removing user decision-making burden
- Secure forms for patient intake and consent documentation
- Access logging supporting audit requirements
The consequences of non-compliance extend beyond financial penalties to professional licensing risks, making specialised healthcare email solutions essential despite potentially higher costs.
Migration Strategies and Implementation
Transitioning to a new email provider involves more than simply opening accounts. In fact, successful migrations require careful planning, clear communication, and systematic execution in order to minimise disruption. Furthermore, a structured approach helps organisations maintain continuity while also reducing the risk of data loss or operational downtime.
Planning Your Transition
Effective migration begins with comprehensive planning:
- Inventory existing email data volume and structure
- Identify critical integrations requiring reconfiguration
- Establish transition timeline with buffer for complications
- Designate internal champions supporting user adoption
- Develop rollback procedures if serious issues emerge
Phased rollouts often prove more manageable than complete cutover migrations. In particular, starting with a small pilot group identifies issues before affecting the entire organisation. Moreover, user feedback from early adopters informs training materials and support resources for broader deployment. As a result, organisations can reduce risk while improving the quality of the final implementation.
Data Migration Considerations
Historical email represents valuable organisational knowledge and legal documentation. Ensuring complete, accurate migration prevents information loss and compliance gaps.
Most secure email providers offer migration tools or services, though capabilities vary significantly. Some organisations prefer working with specialised migration consultants, particularly when moving large data volumes or complex folder structures.
Critical migration elements include:
- Message content and attachments
- Folder hierarchies and organisation systems
- Contact lists and address books
- Calendar entries and meeting histories
- Email rules and filtering configurations
Testing migration processes with non-critical data before committing production information reduces risk. Maintaining temporary access to legacy systems during transition periods provides safety nets if users need historical information.
Privacy and Security Trade-offs
No email solution offers perfect security without any usability compromises. In particular, organisations must consciously decide which trade-offs align with their risk tolerance and operational requirements when selecting a Proton alternative. As a result, this ensures that chosen platforms reflect both security needs and day-to-day usability demands. Moreover, such a balanced approach helps organisations maintain both protection and productivity.
Convenience Versus Protection
Maximum security often requires additional user steps. In particular, entering passwords, managing encryption keys, and verifying recipient identities add friction to communication workflows. As a result, organisations must balance security stringency against user compliance likelihood. Moreover, this balance is essential to ensure that security measures are consistently followed rather than bypassed.
Common trade-off decisions:
- Automatic encryption versus manual key management
- Web-based access versus dedicated application requirements
- Third-party integration support versus isolated security
- Search functionality versus zero-knowledge encryption
- Mobile convenience versus desktop-only access
Understanding user behaviour patterns helps predict which security measures will be followed consistently versus those likely to be circumvented. In particular, designing security around realistic user compliance rather than theoretical perfection produces better practical outcomes. As a result, organisations can improve both adoption rates and overall security effectiveness. Moreover, this approach reduces the likelihood of users bypassing controls in day-to-day workflows.
Transparency and Trust
Provider trustworthiness represents perhaps the most critical security consideration. In particular, even robust technical measures prove worthless if providers themselves cannot be trusted with access to infrastructure and encryption keys. As a result, organisations must carefully evaluate vendor transparency, governance, and security practices. Moreover, this assessment is essential to ensure long-term confidence in the chosen provider.
Evaluating provider credibility involves examining:
- Jurisdiction and legal framework governing operations
- Transparency reports detailing government data requests
- Independent security audits and published results
- Open-source components enabling community verification
- Company ownership structure and funding sources
Providers based in privacy-friendly jurisdictions with strong legal protections offer advantages over those subject to broad surveillance authorities. Various secure email providers operate under different legal frameworks, creating substantially different privacy implications despite similar technical security features.
Emerging Trends in Secure Business Email
The secure email landscape continues evolving rapidly as new technologies emerge and user expectations shift. In particular, understanding these trends helps organisations make forward-looking decisions rather than solving yesterday’s problems. As a result, businesses can adopt solutions that remain relevant over time. Moreover, this proactive approach supports long-term security, adaptability, and operational efficiency.
Artificial Intelligence and Security
AI-powered security features increasingly differentiate modern email providers. In particular, machine learning algorithms detect phishing attempts, identify suspicious patterns, and protect against social engineering attacks with growing sophistication. As a result, organisations benefit from improved threat detection and faster response to emerging risks.
However, AI integration raises privacy questions. For example, training effective security algorithms typically requires analysing message content, potentially conflicting with zero-knowledge encryption principles. Therefore, providers navigate this tension through various technical approaches with different privacy implications.
AI applications in secure email:
- Phishing detection and warning systems
- Spam filtering without content access
- Anomaly detection for account compromise
- Automated threat intelligence integration
Organisations should understand how providers implement AI features and whether these technologies compromise encryption or privacy guarantees. Comprehensive reviews often examine these technical implementation details beyond marketing claims.
Decentralised and Blockchain Approaches
Some newer providers experiment with decentralised architectures and blockchain technologies, promising enhanced security through distributed systems. These approaches eliminate single points of failure and reduce dependence on centralised provider infrastructure.
However, decentralised systems often sacrifice convenience and integration capabilities. The technology remains relatively immature, with questions about scalability, performance, and practical business applicability. Forward-thinking organisations monitor these developments whilst maintaining realistic expectations about current limitations.
Customisation and White-Label Solutions
Larger organisations or those with unique branding requirements may seek customisable email solutions beyond standard consumer offerings. White-label options allow businesses to present secure email under their own branding whilst leveraging provider infrastructure.
Customisation benefits include:
- Consistent branding across all communication channels
- Tailored security policies matching organisational requirements
- Custom integration development with proprietary systems
- Enhanced control over user experience and workflows
These solutions typically command premium pricing but deliver value for organisations where email represents a critical customer touchpoint or competitive differentiator. If you’re exploring comprehensive secure communication solutions, scheduling a demonstration of integrated services can reveal how customised approaches address specific business requirements.
Self-Hosted Alternatives
Some technically sophisticated organisations choose self-hosted secure email rather than third-party providers. This approach offers maximum control and customisation but requires substantial technical expertise and ongoing maintenance investment.
Self-hosting considerations:
| Advantage | Disadvantage |
|---|---|
| Complete data control | Significant technical burden |
| Ultimate customisation | Security responsibility |
| No recurring subscriptions | Infrastructure costs |
| Independence from providers | Limited support resources |
Self-hosting suits organisations with existing IT infrastructure and staff capable of managing complex email security. Smaller businesses typically find managed services more cost-effective and reliable than attempting internal implementation.
Compliance and Regulatory Alignment
Regulatory compliance drives many secure email decisions, particularly in heavily regulated industries. Different jurisdictions and sectors impose varying requirements that email solutions must accommodate.
Regional Data Protection Requirements
GDPR in Europe, CCPA in California, and similar regulations worldwide create specific obligations regarding personal data handling. Email providers must demonstrate compliance through technical measures, contractual commitments, and operational practices.
Key compliance factors:
- Data processing agreements and controller-processor relationships
- Data residency and cross-border transfer restrictions
- Individual rights support (access, deletion, portability)
- Breach notification procedures and timelines
- Processor due diligence and audit rights
Organisations operating internationally face complex compliance landscapes where requirements sometimes conflict. Selecting providers with robust compliance programmes and multi-jurisdictional expertise reduces organisational burden and risk exposure.
Industry-Specific Standards
Beyond general data protection, certain industries face additional specialised requirements. Financial services must address payment card industry standards, healthcare providers navigate medical privacy rules, and government contractors meet security clearance demands.
Finding the right alternative involves matching provider capabilities to your specific compliance obligations. Generic secure email may provide inadequate protection for regulated industries, whilst specialised providers understand nuanced requirements and offer appropriate controls.
Selecting the optimal proton alternative requires balancing security requirements, operational needs, budget constraints, and compliance obligations unique to your organisation. The secure email landscape offers diverse options ranging from privacy-focused minimalist providers to feature-rich business communication platforms. Whether you prioritise maximum encryption strength, seamless integration, regulatory compliance, or cost efficiency, understanding these factors enables informed decisions protecting your communications whilst supporting business objectives. vBoxx delivers secure hosting and cloud solutions designed for businesses requiring robust privacy protections alongside practical functionality, offering email services, encrypted storage, and comprehensive infrastructure supporting modern secure operations.



