The digital transformation accelerating across industries has made secure cloud data storage a critical consideration for organisations worldwide. As a result, as businesses continue to migrate their operations to cloud environments, protecting sensitive information from unauthorised access, data breaches, and compliance violations has become paramount. In this context, understanding the comprehensive security measures, industry standards, and best practices that safeguard cloud-stored data is essential. By doing so, organisations can confidently leverage cloud technology while still maintaining robust protection for their most valuable digital assets.
Understanding the Security Landscape of Cloud Storage
Secure cloud data storage operates on a shared responsibility model, whereby cloud service providers manage infrastructure security, while organisations remain accountable for protecting their data, managing access controls, and ensuring compliance. Therefore, this partnership requires a clear understanding of security boundaries as well as proactive implementation of appropriate protection mechanisms.
Moreover, the shared responsibility framework varies depending on the service model adopted. For example, Infrastructure-as-a-Service (IaaS) requires organisations to manage additional security layers, including operating systems, applications, and data encryption. In contrast, Platform-as-a-Service (PaaS) shifts some responsibilities to providers, while Software-as-a-Service (SaaS) delivers the most managed security environment. Nevertheless, regardless of the model selected, organisations must actively participate in securing their cloud-stored information to maintain robust protection and compliance.
Key Security Threats Facing Cloud Storage
Modern cloud storage environments face sophisticated threats that evolve continuously. Understanding these risks helps organisations implement appropriate countermeasures.
Primary threat categories include:
- Unauthorised access through compromised credentials or weak authentication
- Data breaches resulting from misconfigured storage buckets or inadequate encryption
- Insider threats from malicious or negligent employees with excessive permissions
- Ransomware attacks targeting cloud-stored backups and production data
- Compliance violations stemming from inadequate data governance policies
- Account hijacking through phishing or social engineering tactics

The consequences of security failures extend beyond immediate data loss. Organisations face regulatory penalties, reputational damage, operational disruption, and significant financial costs. According to recent industry analyses, the average cost of a data breach continues to escalate, making preventative security measures considerably more cost-effective than reactive responses.
Encryption Strategies for Maximum Protection
Encryption forms the foundation of secure cloud data storage, transforming readable data into encoded formats that remain unintelligible without proper decryption keys. Implementing comprehensive encryption strategies across multiple layers creates robust protection against unauthorised access.
Encryption at Rest and in Transit
Data requires protection both whilst stored on cloud servers and during transmission between systems. Encryption at rest secures stored files using Advanced Encryption Standard (AES) with 256-bit keys, industry-standard protection that renders data unreadable without authentication. Microsoft outlines comprehensive access controls and encryption practices that organisations should implement across their cloud infrastructure.
Transport Layer Security (TLS) 1.3 protocols protect data moving between users, applications, and cloud storage systems. This encryption prevents interception during transmission, ensuring information remains confidential throughout its journey. Organisations should enforce TLS for all connections, rejecting outdated protocols that contain known vulnerabilities.
| Encryption Type | Purpose | Standard Protocol | Key Strength |
|---|---|---|---|
| At Rest | Protects stored data | AES-256 | 256-bit keys |
| In Transit | Secures data movement | TLS 1.3 | Perfect forward secrecy |
| End-to-End | Client-side protection | User-managed keys | Variable (recommended 256-bit) |
| Database | Column-level security | Transparent Data Encryption | 256-bit keys |
Client-Side Encryption and Key Management
Client-side encryption provides an additional security layer by encrypting data before it reaches cloud storage servers. This approach ensures that even cloud providers cannot access unencrypted information, offering maximum privacy for highly sensitive data.
Effective key management separates encryption keys from encrypted data, storing keys in dedicated Hardware Security Modules (HSMs) or key management services. This separation ensures that compromising storage systems alone does not provide access to encrypted information. Organisations should implement key rotation policies, regularly updating encryption keys whilst maintaining access to previously encrypted data through versioned key management.
Access Control and Identity Management
Controlling who accesses cloud-stored data and under what conditions represents a critical security component. Implementing granular access controls based on the principle of least privilege minimises exposure and reduces breach impact.
Zero Trust Architecture Implementation
Zero trust security models assume no user or system is inherently trustworthy, requiring continuous verification for every access request. This approach eliminates implicit trust based on network location or prior authentication.
Implementing zero trust for secure cloud data storage involves several key components:
- Multi-factor authentication (MFA) requiring multiple verification methods before granting access
- Conditional access policies evaluating user location, device health, and behaviour patterns
- Micro-segmentation dividing cloud storage into isolated zones with separate access controls
- Continuous monitoring analysing user activities for anomalous behaviour indicating compromise
- Just-in-time access providing temporary elevated permissions only when necessary
Identity and Access Management (IAM) systems centralise authentication and authorisation across cloud environments. These platforms enable administrators to define granular permissions, controlling which users access specific files, folders, or storage buckets. Salesforce’s cloud security best practices emphasise strengthening access control through zero trust principles and robust IAM implementation.

Role-Based Access Control (RBAC)
RBAC assigns permissions based on job functions rather than individual users, thereby simplifying administration whilst maintaining strong security controls. For example, marketing teams receive access to campaign assets, finance departments access financial records, and development teams access code repositories, with no unnecessary cross-functional permissions. As a result, organisations reduce the risk of excessive or inappropriate access.
Furthermore, regular access reviews help identify and remove outdated permissions, ensuring that employees retain only the access rights necessary for their roles. In addition, when staff change positions or leave organisations, RBAC systems facilitate rapid permission updates. Consequently, businesses can prevent unauthorised access through dormant or improperly configured accounts.
Compliance Frameworks and Regulatory Standards
Secure cloud data storage therefore must align with industry regulations and compliance frameworks governing data protection. In particular, understanding the applicable standards helps organisations clearly define their security responsibilities. As a result, businesses can meet legal obligations while also implementing proven and structured security practices. Ultimately, aligning storage strategies with recognised frameworks strengthens both compliance and overall risk management.
Key Compliance Standards
Different industries and regions, however, impose specific requirements for data protection. For example, financial services organisations must comply with PCI DSS for payment card data, while healthcare providers follow Health Insurance Portability and Accountability Act in the United States or General Data Protection Regulation across Europe. Similarly, government contractors are required to adhere to frameworks such as FedRAMP or comparable national standards. Consequently, organisations must carefully evaluate which regulations apply to their operations and ensure their cloud data storage strategies align accordingly.
Essential compliance frameworks include:
- GDPR (General Data Protection Regulation) governing personal data of EU residents
- ISO/IEC 27001 providing comprehensive information security management standards
- SOC 2 validating security controls for service organisations
- HIPAA protecting healthcare information in the United States
- PCI DSS securing payment card transaction data
The ISO/IEC 27017 standard specifically addresses cloud security controls, providing guidelines for both cloud service providers and customers. This standard extends ISO/IEC 27001 with cloud-specific recommendations, offering a comprehensive framework for secure cloud operations.
Data Sovereignty and Geographic Controls
Data sovereignty regulations, in particular, require certain types of information to remain within specific geographic boundaries. For instance, financial records, healthcare data, or government information may need to be stored in designated countries or regions in order to comply with local laws. As a result, organisations must carefully assess where their data resides.
Consequently, cloud storage providers offering secure hosting solutions typically maintain multiple data centre locations, thereby enabling organisations to select storage regions that satisfy regulatory requirements. Moreover, geographic redundancy not only strengthens disaster recovery capabilities but also helps maintain compliance with data localisation mandates. Ultimately, this approach balances resilience with regulatory adherence.
Monitoring, Auditing, and Incident Response
Continuous monitoring and comprehensive auditing therefore provide critical visibility into cloud storage activities, enabling rapid threat detection and effective incident response. In particular, proactive security monitoring helps identify suspicious behaviour at an early stage, before it escalates into serious breaches. As a result, organisations can respond more quickly, minimise potential damage, and strengthen their overall security posture.
Security Information and Event Management (SIEM)
SIEM platforms aggregate logs from cloud storage systems, analysing activities for security threats. These tools correlate events across multiple systems, identifying patterns that individual log entries might not reveal.
Effective SIEM implementation for secure cloud data storage includes:
- Centralised log collection from all cloud storage systems and access points
- Real-time analysis of user activities, authentication attempts, and data transfers
- Automated alerting for suspicious behaviours or policy violations
- Integration with threat intelligence feeds for emerging attack patterns
- Forensic capabilities supporting post-incident investigation
Machine learning algorithms enhance SIEM effectiveness by establishing baseline behaviour patterns and flagging deviations. These systems detect insider threats, compromised accounts, or unusual data exfiltration that traditional rule-based monitoring might miss.
| Monitoring Component | Function | Benefit | Implementation Priority |
|---|---|---|---|
| Access Logging | Records all authentication attempts | Identifies unauthorised access | High |
| Data Transfer Monitoring | Tracks file uploads/downloads | Detects data exfiltration | High |
| Configuration Auditing | Monitors security setting changes | Prevents misconfigurations | High |
| User Behaviour Analytics | Analyses activity patterns | Identifies compromised accounts | Medium |
| Compliance Reporting | Documents regulatory adherence | Supports audit requirements | Medium |
Incident Response Planning
Despite preventative measures, organisations must still prepare for potential security incidents. In this context, comprehensive incident response plans outline procedures for detecting, containing, investigating, and recovering from security breaches affecting cloud-stored data.
Moreover, effective incident response for secure cloud data storage requires clearly defined roles, communication protocols, and technical procedures. For example, teams should conduct regular tabletop exercises simulating various breach scenarios, thereby testing response procedures and identifying improvement opportunities. Additionally, documenting lessons learned from both exercises and actual incidents further enhances the organisation’s security posture. Consequently, a proactive and structured approach ensures quicker recovery and stronger protection against future threats.
Backup Strategies and Disaster Recovery
Secure cloud data storage extends beyond protecting against unauthorised access to ensuring data availability and recoverability. Comprehensive backup strategies protect against data loss from technical failures, human errors, malicious attacks, or natural disasters.
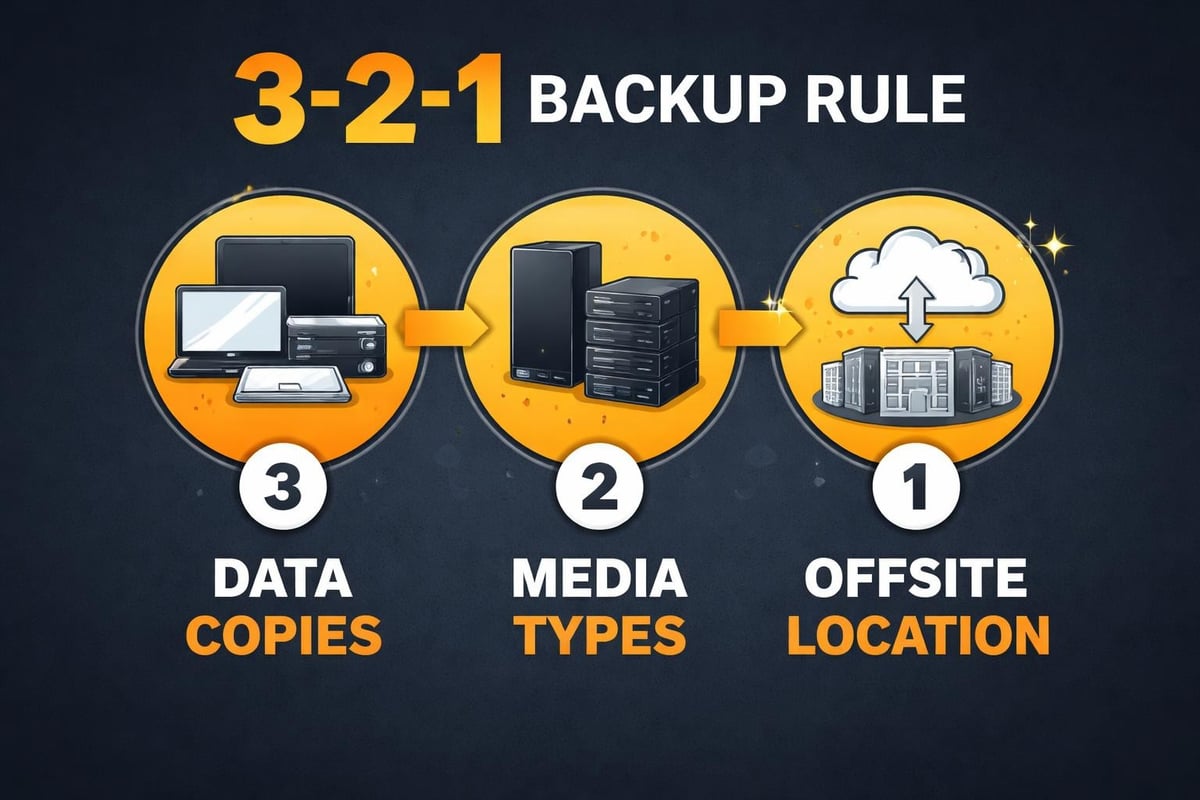
The 3-2-1 Backup Rule
The 3-2-1 rule provides a proven framework for reliable backups: maintain three copies of data, store copies on two different media types, and keep one copy offsite. This approach ensures data survives various failure scenarios.
For cloud environments, the 3-2-1 rule translates to:
- Three copies: Production data, primary cloud backup, secondary backup location
- Two media types: Different cloud storage classes or combination of cloud and on-premises storage
- One offsite: Geographic separation between primary and backup storage locations
Google Cloud recommends specific security measures including encryption with Cloud KMS and uniform bucket-level access to protect backup data. Organisations should apply equivalent or stronger security controls to backups as they apply to production data.
Immutable Backups and Ransomware Protection
Immutable backups cannot be modified or deleted for specified retention periods, thereby protecting against ransomware attacks that target backup systems. As a result, this protection ensures organisations can recover from encryption attacks without paying ransoms.
In practice, implementing immutable backups involves configuring object lock features that prevent deletion or modification until retention periods expire. Furthermore, when combined with versioning capabilities, this approach maintains multiple recovery points while also preventing malicious alteration. In addition, regular recovery testing validates backup integrity and restoration procedures, thereby ensuring that organisations can reliably recover data when needed. Ultimately, these measures strengthen overall data resilience and business continuity.
Advanced Security Technologies
Emerging technologies enhance secure cloud data storage capabilities, offering sophisticated protection mechanisms beyond traditional security measures. Understanding and implementing these technologies positions organisations at the forefront of cloud security.
Artificial Intelligence and Machine Learning
AI-powered security systems therefore analyse vast amounts of data to identify threats that human analysts or rule-based systems might miss. In particular, machine learning algorithms establish normal activity patterns, thereby flagging anomalies that indicate potential security incidents.
Moreover, behavioural analysis examines how users interact with cloud storage, helping to identify unusual patterns such as downloading unexpected data volumes, accessing files outside normal working hours, or attempting to access unauthorised resources. As a result, these indicators may signal compromised accounts or insider threats, which in turn require prompt investigation and remediation. Ultimately, combining AI with behavioural monitoring strengthens overall cloud data security and threat detection capabilities.
Blockchain for Data Integrity
Blockchain technology therefore provides tamper-evident audit trails for cloud-stored data. Specifically, by recording file hashes in distributed ledgers, organisations can verify data integrity and detect unauthorised modifications. As a result, this approach particularly benefits regulated industries that require strong evidence of data authenticity.
Although blockchain implementation adds complexity, it nevertheless offers compelling advantages for scenarios requiring absolute proof of data integrity, such as legal documents, financial records, or medical imaging. Moreover, combining blockchain with traditional cloud security measures can enhance trust, transparency, and accountability in sensitive data management.
Data Loss Prevention and Classification
Data Loss Prevention (DLP) systems monitor data movements, preventing unauthorised transfers of sensitive information from secure cloud data storage. These technologies identify, classify, and protect confidential data based on content analysis and policy rules.
Automated Data Classification
Machine learning-based classification systems therefore scan files uploaded to cloud storage, automatically applying appropriate security labels. For example, personal identifiable information triggers privacy controls, financial data receives compliance tags, and intellectual property is assigned additional access restrictions. As a result, organisations can enforce security measures consistently based on data type and sensitivity.
Moreover, classification enables policy enforcement that adapts security controls according to data sensitivity. For instance, highly classified information might require encryption, geographic restrictions, and approval workflows for sharing, whereas public information flows freely. Consequently, organisations should implement classification schemes that align with their risk profiles and regulatory requirements, thereby strengthening overall data protection.
Content Inspection and Policy Enforcement
DLP systems inspect file contents, metadata, and context to identify policy violations. Attempting to share files containing credit card numbers externally triggers alerts or blocks the action entirely. Email attachments containing confidential markings require additional authentication before transmission.
Policy enforcement extends to file storage services through integration with cloud storage APIs. These integrations enable real-time monitoring and control over data movements, preventing accidental or malicious information disclosure.
Performance and Security Balance
Implementing comprehensive security measures for secure cloud data storage must not compromise performance or user experience. Organisations need strategies that deliver robust protection whilst maintaining operational efficiency.
Optimising Encryption Performance
Modern processors include hardware acceleration for encryption operations, minimising performance impact. Cloud providers leverage these capabilities, ensuring encryption and decryption occur with negligible latency. Organisations should select cloud storage services utilising hardware-accelerated encryption for optimal performance.
Caching encrypted data at edge locations reduces retrieval times whilst maintaining security. Content delivery networks (CDNs) with encryption support enable fast global access to protected content without exposing unencrypted data.
| Security Measure | Performance Impact | Mitigation Strategy | User Experience Effect |
|---|---|---|---|
| Encryption | Minimal with hardware acceleration | Use AES-NI processors | Transparent |
| MFA | Slight authentication delay | Implement SSO and remember devices | Acceptable |
| DLP Scanning | Moderate for large files | Asynchronous scanning | Background process |
| Access Logging | Negligible | Efficient log aggregation | Transparent |
| Geo-restrictions | Potential latency | Regional data centres | Location-dependent |
User Experience Considerations
Security measures that frustrate users encourage workarounds that compromise protection. Single Sign-On (SSO) reduces authentication friction whilst maintaining security through centralised identity management. Risk-based authentication adjusts security requirements based on context, requiring additional verification only for unusual activities.
Transparent security controls that operate behind the scenes deliver protection without impacting workflows. Users benefit from comprehensive security without constant authentication prompts or access delays.
Vendor Selection and Due Diligence
Choosing cloud storage providers requires careful evaluation of security capabilities, compliance certifications, and operational practices. Organisations entrust providers with their most sensitive information, making vendor selection a critical security decision.
Security Assessment Criteria
Comprehensive vendor assessment examines technical capabilities, certifications, policies, and track record. Providers should maintain relevant compliance certifications (SOC 2, ISO 27001, industry-specific standards), demonstrate encryption capabilities, and offer granular access controls.
Transparency regarding security practices, incident history, and breach notification procedures indicates responsible providers. Cloud Security Alliance best practices emphasise understanding the shared responsibility model and knowing how providers access and store data.
Service Level Agreements and Data Ownership
SLAs should clearly define security responsibilities, uptime guarantees, breach notification timelines, and support response times. Data ownership clauses must confirm organisations retain full ownership of their information, with providers prohibited from accessing or using data beyond service delivery.
Exit strategies enabling data extraction and account termination prevent vendor lock-in. Organisations should verify they can retrieve complete data sets in usable formats should they change providers or migrate to alternative infrastructure.
Continuous Improvement and Security Evolution
Secure cloud data storage requires ongoing attention as threats evolve and technologies advance. Organisations must establish processes for continuous security improvement, adapting protections to address emerging risks.
Regular Security Assessments
Quarterly or annual security assessments evaluate control effectiveness, identify vulnerabilities, and recommend improvements. These assessments should include penetration testing, configuration reviews, access audits, and policy evaluations.
Third-party security assessments provide objective evaluations of security posture. External auditors bring fresh perspectives, identifying blind spots internal teams might miss through familiarity with existing systems.
Security Awareness Training
Human factors significantly impact security effectiveness. Regular training ensures employees understand secure cloud data storage practices, recognise phishing attempts, and follow established security procedures. Training should cover password management, MFA usage, data classification, and incident reporting.
Simulated phishing campaigns test awareness whilst identifying users requiring additional training. Metrics tracking training completion, phishing test results, and policy compliance guide continuous improvement efforts.
Protecting information in cloud environments requires comprehensive strategies combining encryption, access controls, monitoring, and compliance frameworks. Organisations implementing these secure cloud data storage practices position themselves to leverage cloud benefits whilst maintaining robust protection for sensitive information. vBoxx delivers enterprise-grade secure hosting and cloud solutions with privacy-focused architecture, compliance certifications, and green hosting practices, helping businesses protect their digital assets whilst supporting sustainable operations. Contact vBoxx today to discover how our secure cloud infrastructure can safeguard your organisation’s most valuable data.



